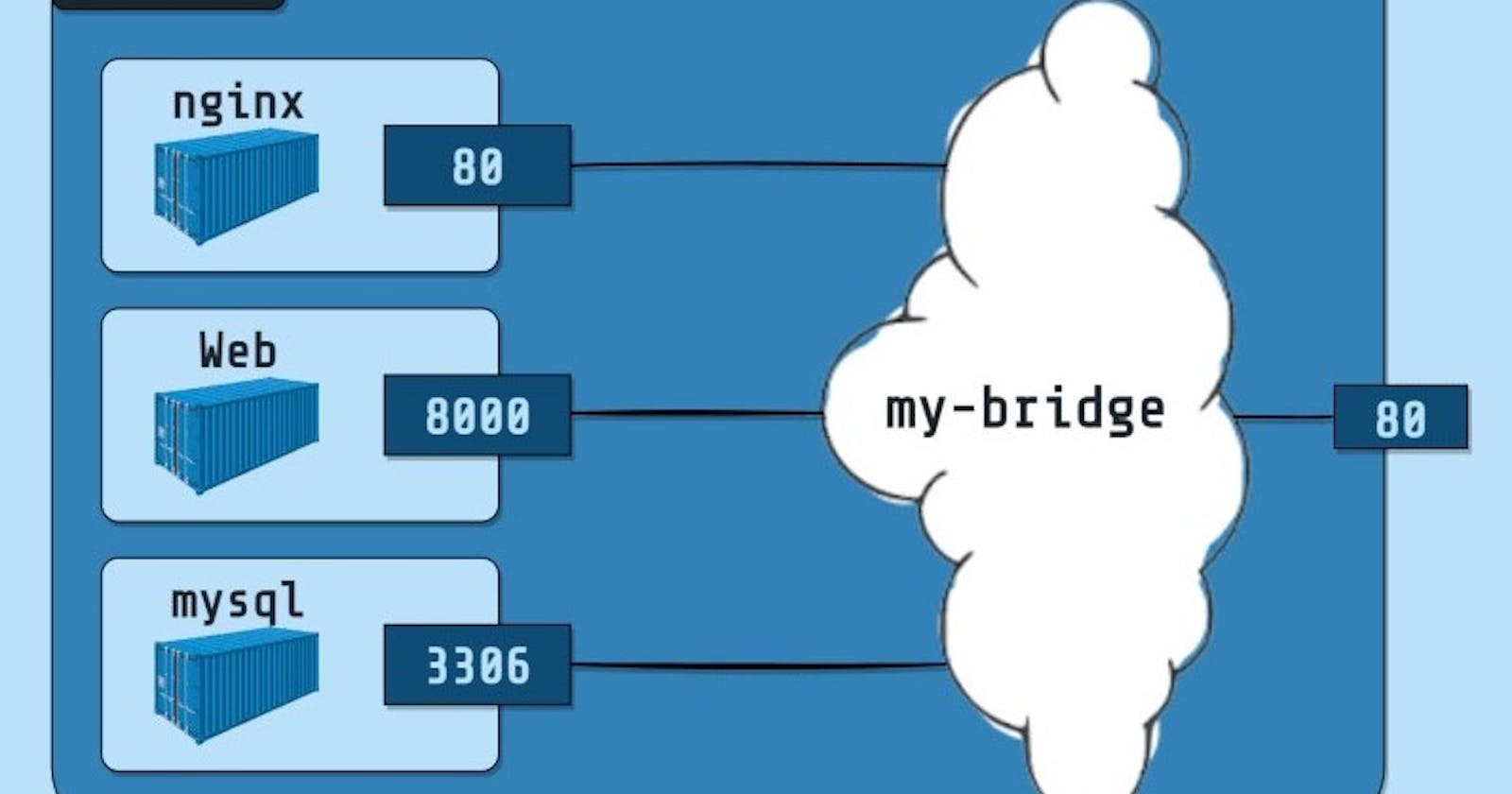
Bridge network is a default network created automatically when you deploy a container. Bridge network uses a software bridge that allows containers connected to the same bridge network to communicate. Bridge networks used on containers that are running on the same Docker daemon host. The bridge network creates a private internal isolated network to the host so containers on this network can communicate.
In terms of networking, a bridge network is a Link Layer device which forwards traffic between network segments. A bridge can be a hardware device or a software device running within a host machine’s kernel.
In terms of Docker, a bridge network uses a software bridge which lets containers connected to the same bridge network communicate, while providing isolation from containers that aren’t connected to that bridge network. The Docker bridge driver automatically installs rules in the host machine so that containers on different bridge networks can’t communicate directly with each other.
When you start Docker, a default bridge network (also called bridge) is created automatically, and newly-started containers connect to it unless otherwise specified. You can also create user-defined custom bridge networks. User-defined bridge networks are superior to the default bridge network.
👉 Differences between user-defined bridges and the default bridge
User-defined bridges provide automatic DNS resolution between containers:
Containers on the default bridge network can only access each other by IP addresses, unless you use the
--linkoption, which is considered legacy. On a user-defined bridge network, containers can resolve each other by name or alias. Imagine an application with a web front-end and a database back-end. If you call your containerswebanddb, the web container can connect to the db container atdb, no matter which Docker host the application stack is running on.If you run the same application stack on the default bridge network, you need to manually create links between the containers (using the legacy
--linkflag). These links need to be created in both directions, so you can see this gets complex with more than two containers which need to communicate. Alternatively, you can manipulate the/etc/hostsfiles within the containers, but this creates problems that are difficult to debug.
User-defined bridges provide better isolation:
All containers without a
--networkspecified, are attached to the default bridge network. This can be a risk, as unrelated stacks/services/containers are then able to communicate.Using a user-defined network provides a scoped network in which only containers attached to that network are able to communicate.
Containers can be attached and detached from user-defined networks on the fly:
- During a container’s lifetime, you can connect or disconnect it from user-defined networks on the fly. To remove a container from the default bridge network, you need to stop the container and recreate it with different network options.
Each user-defined network creates a configurable bridge:
If your containers use the default bridge network, you can configure it, but all the containers use the same settings, such as MTU and
iptablesrules. In addition, configuring the default bridge network happens outside of Docker itself, and requires a restart of Docker.User-defined bridge networks are created and configured using
docker network create. If different groups of applications have different network requirements, you can configure each user-defined bridge separately, as you create it.
Linked containers on the default bridge network share environment variables:
Originally, the only way to share environment variables between two containers was to link them using the --link flag. This type of variable sharing isn't possible with user-defined networks. However, there are superior ways to share environment variables.
Multiple containers can mount a file or directory containing the shared information, using a Docker volume.
Multiple containers can be started together using
docker-composeand the compose file can define the shared variables.You can use swarm services instead of standalone containers, and take advantage of shared secrets and configs.
👉 Manage a user-defined bridge
Use the docker network create command to create a user-defined bridge network.
$ docker network create my-net
👉 Connect a container to a user-defined bridge
When you create a new container, you can specify one or more --network flags. This example connects an Nginx container to the my-net network. It also publishes port 80 in the container to port 8080 on the Docker host, so external clients can access that port. Any other container connected to the my-net network has access to all ports on the my-nginx container, and vice versa.
$ docker create --name my-nginx \
--network my-net \
--publish 8080:80 \
nginx:latest
To connect a running container to an existing user-defined bridge, use the docker network connect command. The following command connects an already-running my-nginx container to an already-existing my-net network:
$ docker network connect my-net my-nginx
👉 Disconnect a container from a user-defined bridge
To disconnect a running container from a user-defined bridge, use the docker network disconnect command. The following command disconnects the my-nginx container from the my-net network.
$ docker network disconnect my-net my-nginx